We've heard of this but
with few details.
Mark Rumold writes:
For
almost two years, EFF has been fighting
the government in federal court to force the public release of an
86-page opinion of the secret Foreign Intelligence Surveillance Court
(FISC). Issued in October 2011, the secret court’s opinion found
that surveillance conducted by the NSA under the FISA Amendments Act
was unconstitutional and violated “the spirit of” federal law.
Today,
EFF can declare victory: a federal court ordered the government to
release records in our litigation, the government has indicated
it intends to release the opinion today, and ODNI has called a
3:00 EST press conference to discuss “issues” with FISA
Amendments Act surveillance, which we assume will include a
discussion of the opinion.
Read more on EFF.
Update 1:
The opinion can be found here.
The problem seems to have stemmed from “upstream” collection of
data which often collected internet transactions that were neither
to/from approved target facilities nor about targeted facilities.
The upstream collection of Internet transactions accounted for 9% of
the collection.
Update 2:
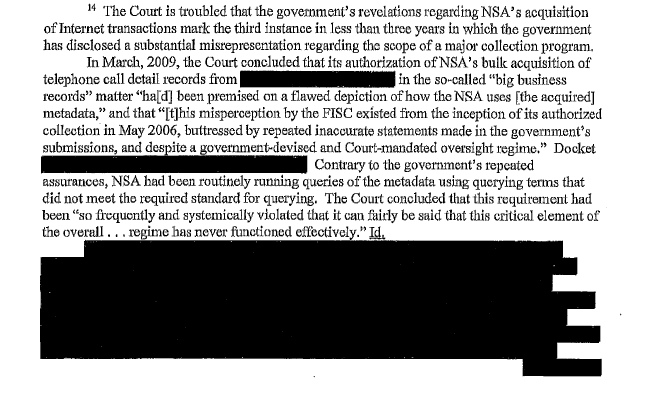
FISC wasn’t too happy with appears to be yet another – and
significant – misrepresentation in previous submissions by the
government:
Update 3:
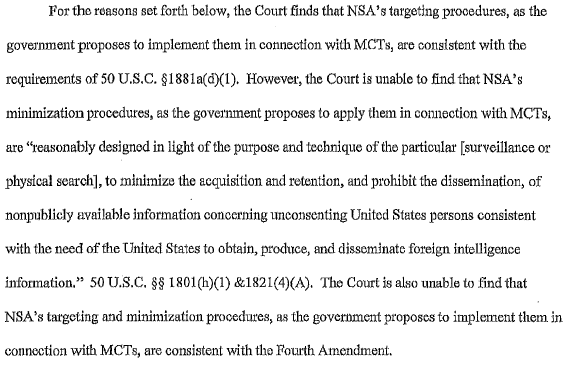
And here we go, from p. 29 of the opinion:
Update 4:
Read more about the opinion in Spencer
Ackerman’s report and in Marcy Wheeler’s commentary here.
(Related)
New
Zealand has passed a hotly-disputed bill that radically expands the
powers of its spying agency. The legislation was passed 61 votes to
59 in a move that was slammed by the opposition as a death knell for
privacy rights in New Zealand.
The
new amendment bill gives the Government Communications Security
Bureau (GCSB) – New Zealand’s version of the NSA – powers to
support the New Zealand police, Defense Force and the Security
Intelligence Service.
Read more on RT.
A useful summary for my
Computer Security students.
A good thing? Do we
need new laws everytime we update the hardware? Seems like the law
should set strategy and the hardware and software are just tactical
variations. Massachusetts
Supreme Court Says Wiretap Statute Applies To Cell Phones
Greg McNeal reports:
The
Supreme Judicial Court of Massachusetts recently ruled
that a judge possesses the authority under the Massachusetts wiretap
statute to issue warrants permitting the interception of cell phone
calls and text messages, despite the fact that both forms of
communication are not mentioned in the Massachusetts wiretap statute.
Read more on Forbes.
Mess with our secrets
will you.
Glenn Greenwald’s
partner, David Miranda, has put the UK government on notice that he
is challenging his detention under Section 7 of the Terrorism Act of
2000 and the seizure of his devices at Heathrow airport this past
weekend.
The detention of
Greenwald’s domestic partner, who has assisted Greenwald in his
work at times, created a storm of protest on the Internet over
government’s seizure of “journalistic materials” Miranda was
carrying between Laura Poitras in Germany and Greenwald in Brazil.
Miranda is a Brazilian citizen.
The files were
reportedly encrypted, but Miranda, who was reportedly not permitted
to consult with a lawyer of his choosing during his almost-9 hour
detention, says he felt coerced into providing the password for fear
he’d be jailed. [What would have happened if he
didn't know the password? Bob]
Carl Gardner provides
his legal analysis of the detention on Head
of Legal.
The law firm of Binders
LLP is representing Miranda, and a copy of their letter to the Home
Office can be found here.
Not everyone found the
detention concerning. Former MP Louise Mensch defended
the government’s action. At the risk of summarizing her
incorrectly, her argument boiled down to: (1) Miranda was not just
traveling as an uninvolved spouse or family member – his trip was
paid for by The Guardian precisely because he was assisting Greenwald
with his work, [How did they know that? Bob] (2) Miranda was
transporting encrypted files containing material stolen from the
government (but that would be our government, not hers), and (3)
Greenwald knew all along that Miranda was carrying files that
contained stolen material. What’s not clear to me from her
argument, however, is how the UK government has any authority to
detain someone carrying stolen files about another government that
may not reveal anything about the UK at all. Snowden has been
charged with theft here, but no one has been charged with receipt or
possession of stolen materials. So what is the real basis for
detaining Miranda? And if it had been Greenwald passing through
Heathrow, would they have had the right to detain him on the basis
that he might be carrying files or work materials?
Frankly, it makes
little sense to me that Miranda was carrying any files, encrypted or
not. Obviously, they would not be the only copies of the files, but
still….
Is this always true?
If so, what implications for lawyers or psycologists or doctors?
(Isn't this why they invented external storage devices?)
From
FourthAmendment.com:
Defendant
took his computer to Staples for a computer tech to remove viruses
and spyware, giving the tech the password to the computer. The
computer tech found child pornography in a folder called “PVT,”
and he called the police who saw the files and seized the computer.
The court finds that the defendant waived his reasonable
expectation of privacy in the computer by his actions.
Read more on
FourthAmendment.com.
I wonder what that
Tennessee court would say about repair people copying nude photos of
a computer owner from a private folder on the drive and then
uploading them to the Internet. Would the judge still hold that the
computer owner had waived REP by giving the repair people the
computer and password?
Interesting?
Arnold Roosendaal has
uploaded his doctoral dissertation, conducted at Tilburg University,
to SSRN. Here’s the abstract:
Every
individual is represented in digital form in numerous data
sets. Commercial companies use these digital representations as a
basis for making decisions that affect the individual. This has
implications for privacy and autonomy of the individual and the
ability to construct one’s own identity. This study describes how
digital representations are created and for what purposes. An
analysis is made of the implications this has for individuals and why
privacy, autonomy, and identity construction are at stake. In
this context legal protection of individuals is provided by data
protection legislation. The current framework, however,
appears to be insufficient in relation to the problems identified in
this study. Other legal constructs are assessed to see whether
alternative approaches could help offer legal protection. Finally, a
proposal is presented to embed the concepts of digital personae and
profiles (as forms of digital representations) as portraits in data
protection law.
You can download his
dissertation (312 pp, pdf) from SSRN.
Perspective I doubt
Google is doomed, but
Wait,
what? Yahoo tops Google in US traffic
For the first time in
five years, Google is no longer No. 1 in US Internet traffic, and its
top spot was taken by a surprising competitor -- the once lackluster
Yahoo.
ComScore released its
monthly report on the top 50 US Internet properties Wednesday and
it listed Yahoo as the top dog in July with 196,564,000 visits.
Google, lagging behind slightly, had 192,251,000.
Marketing
Land noted that Google has been No. 1 since April 2008. While
Yahoo's numbers fluctuated, reaching the No. 2 or No. 3 position
occasionally, but never making it to the top.
… Whether it's some
clever number crunching or a real renewed interest from consumers,
these latest figures have got to give Yahoo CEO Marissa Mayer, and
the company's loyal employees, a good morale boost.
For a few selected
individuals...
A
Complete Guide to Using Blogger In School - 81 Page Free PDF
Since 2006 I have used
Blogger for many blogging projects including this blog and many
classroom blogs. Over the years I've introduced many teachers to
blogging through Blogger. Blogger is easy to use and flexible enough
to support you when you're ready to start using some advanced
blogging strategies. I've covered the basics of Blogger and blogging
in various blog posts over the years. This week I finally put all of
those posts together with a series of annotated screenshots in one
cohesive package, A Complete Guide to Using Blogger In School.
A Complete Guide to
Using Blogger In School covers everything from blogging
terminology to blogging activities to the nuts and bolts of using
Blogger. You'll learn where to find media to use in blog posts, how
to use media in blog posts, and get ideas for media-based blog posts.
You'll also learn how to set-up your blog for multiple authors and
how to manage comments.
A Complete Guide to
Using Blogger In School is embedded below. (The file is hosted
on Box.com, if you cannot see the document embedded below make sure
that your filter isn't blocking Box.net. You may also need to be
using Chrome or a recent version of Firefox, Safari, or IE as
outdated browsers may not support the Box viewer).
I'm going to allow
downloading the guide for the rest of the month. Downloads should be
for personal, non-commercial use. Please do not redistribute it,
including for workshops / faculty training, without my permission.
I've used Box.net to host the file (81 page pdf). Box does not put
advertising on the page while still allowing me to track downloads.
I can has Fair Use?
New
Infographic: Good News in Fair Use for Libraries
“A new infographic
released today tells the story of library fair use and the Code
of Best Practices in a clear and compelling way. There’s an
embeddable
PNG for your own blogs, and there’s also a print-ready
8.5” x 11” version in case you need hardcopies to hand out at
events.”
For all my students.
You do remember me saying something similar? Hello? Anyone there?
(Number 6: Activate cattle prod!)
No comments:
Post a Comment