Articles like this make
me wonder how many centuries it took humans to realize that closing
and locking a door reduced theft? Somewhere these people must have
heard about encrypting data or storing it on a more secure server
locked in a more secure room. Here's a simple idea. Ask your
neighbors, competitors, auditors, even you local police department
about security. Hell, you can even Google it!
Peter Frost and Julie
Wernau of the Chicago Tribune report
than 4 million patients of Advocate Medical Group
may be at risk of ID theft after four computers were stolen during a
burglary last month at Advocate’s administrative building on West
Touhy Avenue in Park Ridge. Advocate Medical Group is part of
Advocate Health Care.
In its statement on
patientnotice.org, a web site it created about the breach, Advocate
explains that the burglary, which occurred overnight, was
discovered on July 15.
Our
investigation confirmed that the computers contained patient
information used by Advocate for administrative purposes and may have
included patient demographic information (for example, names,
addresses, dates of birth, Social Security numbers) and limited
clinical information (for example, treating physician and/or
departments, diagnoses, medical record numbers, medical service
codes, health insurance information). Patient
medical records were not on the computers and patient care
will not be affected. [Aren't “diagnoses'” and
“medical service codes” (tests or treatments they plan to bill
for) “medical records?” Bob]
That sounds like more
than enough information for ID theft and possibly medical ID theft if
the insurance information included policy numbers. Although the
burglars may have stolen the hardware for its non-content value, will
someone discover what is on it and try to misuse the patient
information?
And did Advocate have
enough security in place? The Chicago Tribune reports:
The
building was not equipped with an alarm, but it had a security camera
and a panic button, Golson said. Advocate has since installed
continuous security staffing at the office and is re-evaluating its
security systems and practices systemwide.
The
lack of encryption is probably the most glaring security failure.
Did their policies require encryption but the policies weren’t
followed or did they not have an encryption policy in place? And
will HHS see this as insufficient physical security and insufficient
technical security?
What will HHS do? And
what will the state attorney general do?
A copy of Advocate’s
patient notification letter has been uploaded to the California
Attorney General’s breach reporting site, here
(pdf).
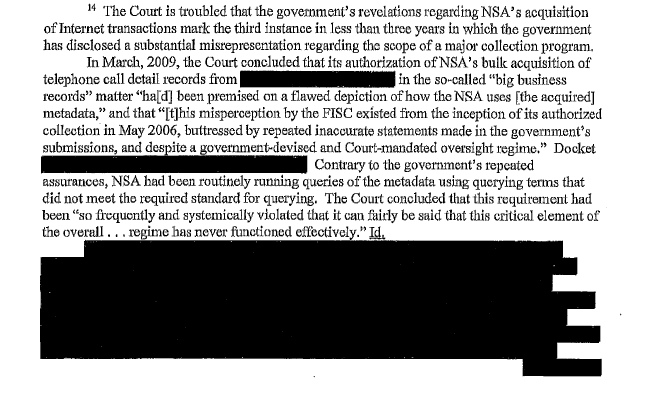
The early poster boy
for illegal surveillance?
New
Zealand appears to have used NSA spy network to target Kim Dotcom
A new examination of previously published affidavits from the
Government Communications Security Bureau (GCSB)—the New Zealand
equivalent of the National Security Agency (NSA)—appears to suggest
that the GCSB used the “Five Eyes” international surveillance
network to capture the communications of Kim Dotcom, the founder of
Megaupload.
The new analysis was
posted
by New Zealand journalist Keith Ng in a Thursday blog post. If the
link proves to be true, it would seem that the NSA’s vast
international surveillance capability can be turned against
individuals unrelated to the NSA’s stated
mission to aid military, counterintelligence, or counterterrorism
objectives.
… At the time of
the surveillance against Dotcom, the GCSB was only allowed to engage
in surveillance of non-resident foreigners. However, earlier this
week, the New
Zealand parliament voted 61-59 to expand the GCSB’s powers to
encompass citizens and legal residents.
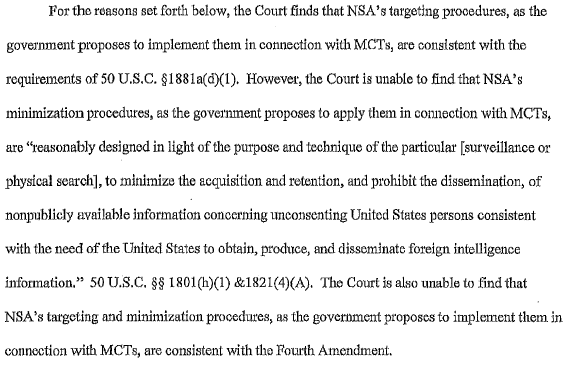
What “privacy
controls” need to be applied at what points in the surveillance
process?
International
Principles on the Application of Human Rights to Communications
Surveillance
by Sabrina
I. Pacifici on August 23, 2013
Final
version 10 July 2013 -International
Principles on the Application of Human Rights to Communications
Surveillance:
“As technologies that
facilitate State surveillance of communications advance, States are
failing to ensure that laws and regulations related to communications
surveillance adhere to international human rights and adequately
protect the rights to privacy and freedom of expression. This
document attempts to explain how international human rights law
applies in the current digital environment, particularly in light of
the increase in and changes to communications surveillance
technologies and techniques. These principles can provide civil
society groups, industry, States and others with a framework to
evaluate whether current or proposed surveillance laws and practices
are consistent with human rights. These principles are the outcome
of a global consultation with civil society groups, industry and
international experts in communications surveillance law, policy and
technology.
Preamble: Privacy is a fundamental human right, and is central to
the maintenance of democratic societies. It is essential to
human dignity and it reinforces other rights, such as freedom of
expression and information, and freedom of association, and is
recognised under international human rights law. Activities that
restrict the right to privacy, including communications surveillance,
can only be justified when they are prescribed by law, they are
necessary to achieve a legitimate aim, and are proportionate to the
aim pursued.
Before
public adoption of the Internet, well-established legal principles
and logistical burdens inherent in monitoring communications created
limits to State communications surveillance. In recent decades,
those logistical barriers to surveillance have decreased and the
application of legal principles in new technological contexts has
become unclear. The explosion of digital communications content
and information about communications, or “communications metadata”
— information about an individual’s communications or use of
electronic devices — the falling cost of storing and mining large
sets of data, and the provision of personal content through third
party service providers make State surveillance possible at an
unprecedented scale. Meanwhile, conceptualisations of existing human
rights law have not kept up with the modern and changing
communications surveillance capabilities of the State, the ability of
the State to combine and organize information gained from different
surveillance techniques, or the increased sensitivity of the
information available to be accessed.”
Clearly, I'm not the
only one who sees this as a good thing.
Steve
Ballmer just made $625 million by firing himself
Since Steve Ballmer’s
announcement this morning that he’s stepping down as CEO of
Microsoft in the next 12 months, the company’s stock has popped
more
than 8%. Ballmer is Microsoft’s second-largest individual
shareholder, with 333,252,990 shares, which means his $16 billion net
worth just
appreciated $625 million. Bill Gates, Microsoft’s largest
individual shareholder, just added $741 million to his $71.3 billion
kitty.
For my website
students.
– helps you to test
web fonts on any website on the fly. Enter the site URL, and when
you click on a font, you will be taken to that website with all of
the text changed to the font you chose. This will allow you to see
right away what a font would look like on your site without having to
actually change anything. You can go back and choose another font
until you find one you like.
Something for my
website students (who have adequate legal representation)
– is a site that
lists, catalogues, and embeds YouTube videos which are full length
feature movies, uploaded by other people. You can break down the
selection by decade, genre, and movie score, and when you click on a
movie poster, that film will be embedded on the page. The
site breaks no laws [Always a “red flag” phrase Bob]
because it is only listing what others have uploaded, and they give a
link if anyone wants to file a copyright violation with YouTube.
What amusements await?
… Facebook
CEO Mark Zuckerberg asked this week if “connectivity
is a human right?” launching, as part of his company’s
mission to “make the world more open and connected,” a new
organization, Internet.org,
to bring the Internet to those in the world without access to it. UC
Berkeley grad student Jen Schradie has a wonderful response in
which she thoroughly trounces the “Silicon Valley ideology”
driving the announcement, which certainly seems much less about
humanitarianism and much more about monetizing a new market.
… It’s the time
of year for the Beloit
Mindset list, which Beloit College publishes each fall
to characterize the “mindset” of incoming freshmen. But even
better, I’d say, was the unveiling of the Benoit
Mindlessness site this week, “dedicated to the mockery and
eventual destruction of the Beloit mindset list.” Also fairly
awesome: the #2170BeloitMindset hashtag on Twitter, with such gems as
“the
planet earth has always been uninhabitable.”
… According to a
survey by CarringtonCrisp, “fifty per cent of
employers would not consider recruiting someone who had studied for
their degree wholly online.” Other findings suggest
that students are “suspicious of MOOCs,”
although less so about online education in general. The
(Pearson-owned) Financial Times, in reporting this “research,”
calls it a “blow to MOOCs.”
… The
Computer Science Teachers Association has released a report
about CS teacher certification in the US, which finds only two states
(Arizona and Wisconsin) require teachers to be certified or licensed
to teach computer science.
… Lots of facts and
figures in The Chronicle of Higher Education’s “Almanac
of Higher Education 2013”: what professors make, what
colleges cost, what students think about digital textbooks, and more.